Building tools to prevent unauthorised access has always been crucial to our strategy. But for many people, it is always a tussle between security and convenience. Amid several recent news stories of data breaches from within art organisations, you may be wondering if your business is doing enough to keep your data secure. Here are some steps you can take to ensure that your information is protected.
1. Restrict access unapologetically
You want to trust the people in your team, but you don't want to pick up the pieces if someone leaves your data exposed or steals your mailing list. So it is probably time for you to check that you have given each of your colleagues access to the parts of your systems that their role, length of service and your trust level permits. It sounds obvious, but you need to plan this out and do the right thing instead of the easy thing. It means restricting access unapologetically to systems and functions that are not necessary for each colleague's role, and it requires conversations about where they fit into the team, what you consider best practice and your comfort level.
Being safe instead of sorry means a bit more administration from trusted senior staff to get things done. User identities for critical systems should never be shared or generic. In Artlogic, your searching, flags, modification history (audit trail) and other vital functions will not work correctly if login details are shared between two or more people. Please keep the number of system administrators (who have super-user privileges) to the minimum and make sure that they know your intentions and that everyone knows who the administrators are. Administrator roles should only be given to the most highly trusted members of the team who are also highly computer literate and trained in how to use the system.
2. Overcome the password hurdle
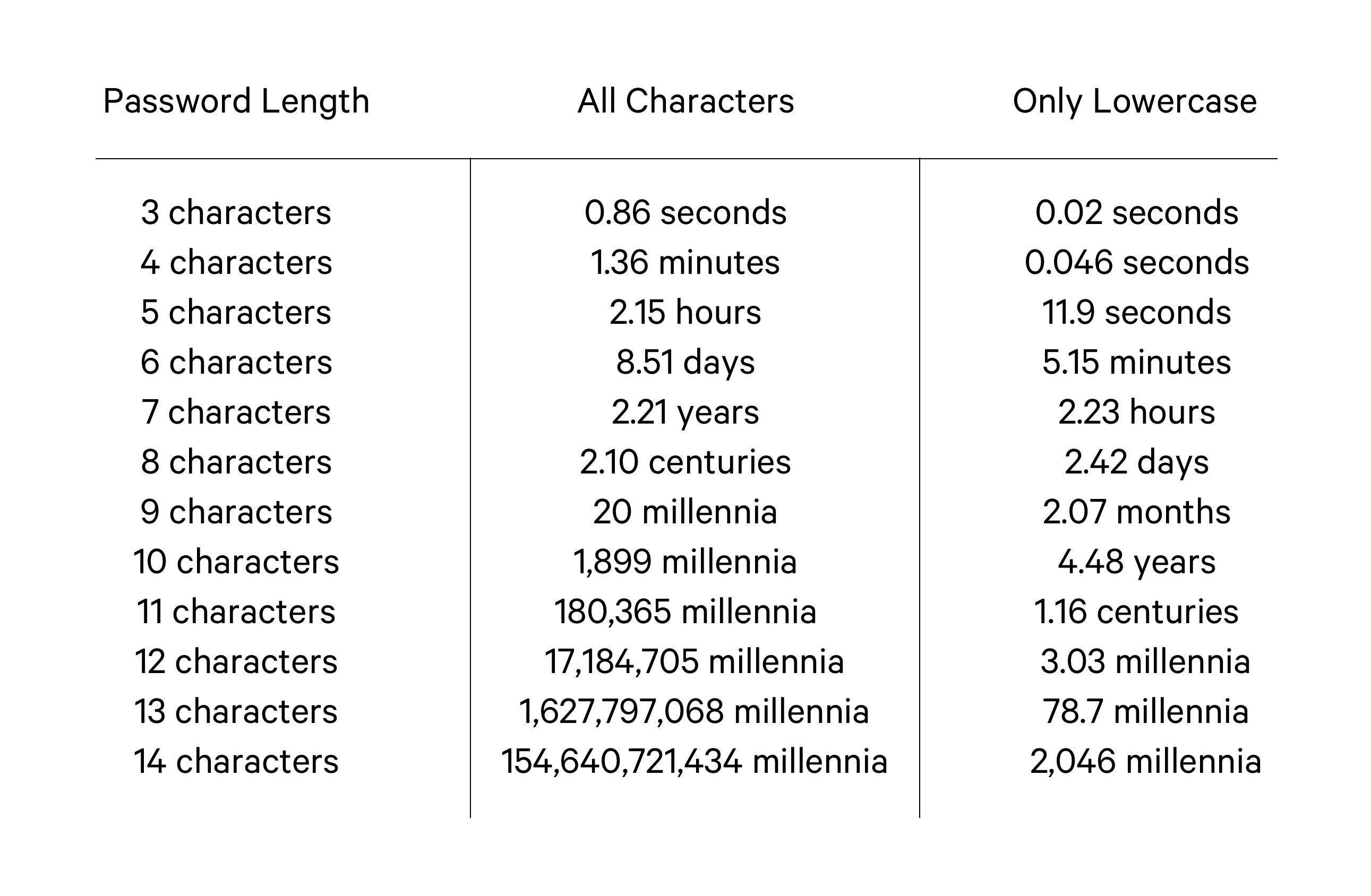
We all know that passwords need to be strong, but sometimes this can be a considerable hurdle for businesses to overcome. We hope that nobody reading this uses any passwords that are on this list, but we know from experience that these have been used by our clients. Passwords should never be shared. For maximum security, you should rotate your passwords every few months. The Artlogic user list screen can help you identify problems by highlighting weak passwords. You can also use password managers such as 1Password, to help you and your team securely store passwords, avoid endless password resetting and writing down passwords in notebooks.
Here is a helpful chart illustrating how quickly passwords can be hacked.
Take these final two steps in Artlogic to prevent unauthorised access even if someone has a username and password.
3. Two-factor authorisation (2FA)
It can sometimes seem annoying to start with, but it is crucial for anyone who travels around or works from home. To get going, download the free Google Authenticator app from the iOS App Store / Google Play Store onto your phone and add a new service, scan the code and enter the number to pair it. From now on, each time you sign in to Artlogic on a new computer or tablet, you need to authenticate it with the app on your phone and renew this every 30 days.
4. Network address protection
Set the IP addresses or ranges where users are allowed access to your systems. If some colleagues only need to access the system from within the gallery, lock the system down to that network for those users, and this would prevent access to anyone outside the gallery, even if they had valid login details. This could even apply to remote workers or people travelling if they used a VPN service that provides them with a dedicated and fixed IP which could be added to the trusted list. There are sometimes some speed reductions so it might be best to experiment with different providers.
Further reading
With the increase in remote working and the greater use personal equipment you might want an IT health check.
See our help note about IT basics and avoiding cybercrime
Find out more about our security features in our database